Incident Management
End-to-end incident lifecycle management from reporting to investigation to closure.
Respond Faster. Investigate Deeper. Prevent Recurrence.
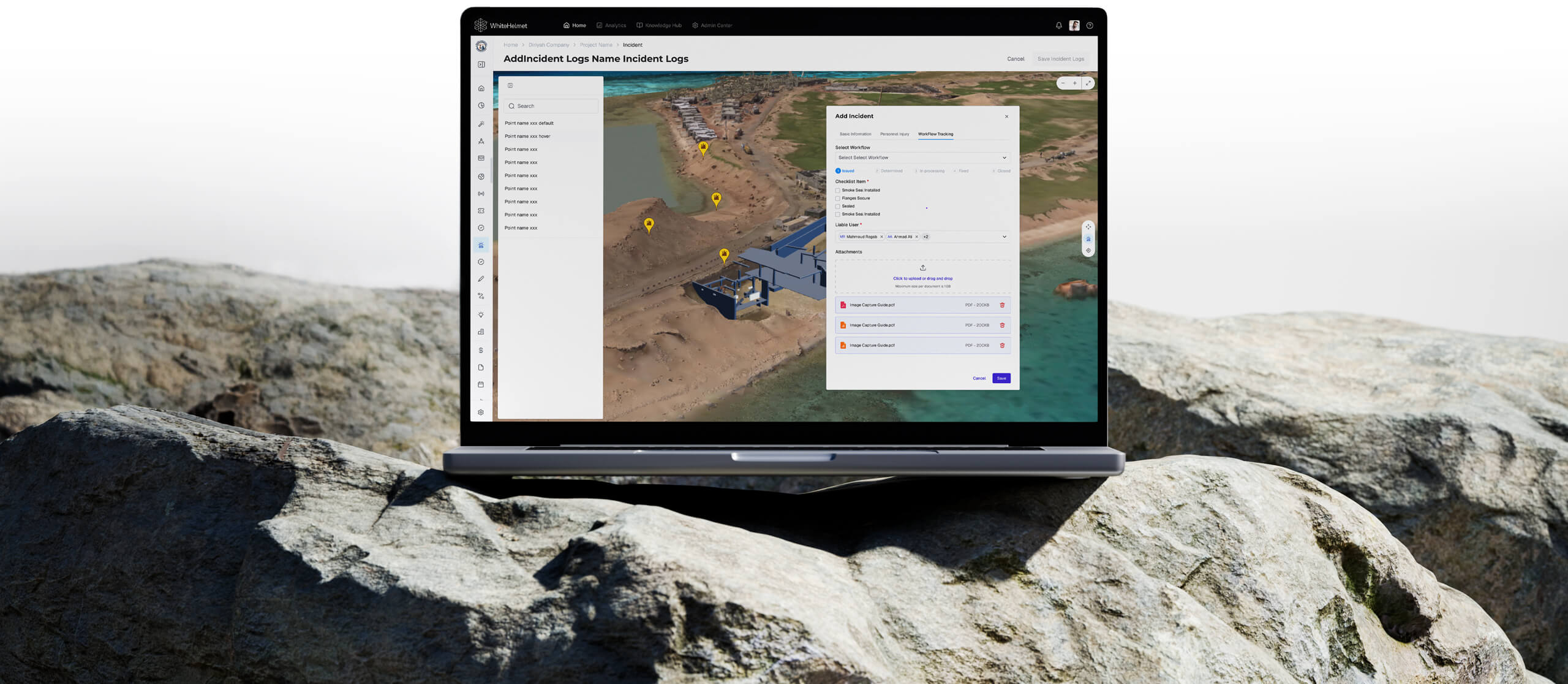
Digitize your entire incident lifecycle — from initial report and geo-tagged documentation through SOP-driven investigation workflows to corrective actions and closure. Incident Management ensures every incident is handled consistently and patterns are identified to take preventive action.
Digital Incident Reporting
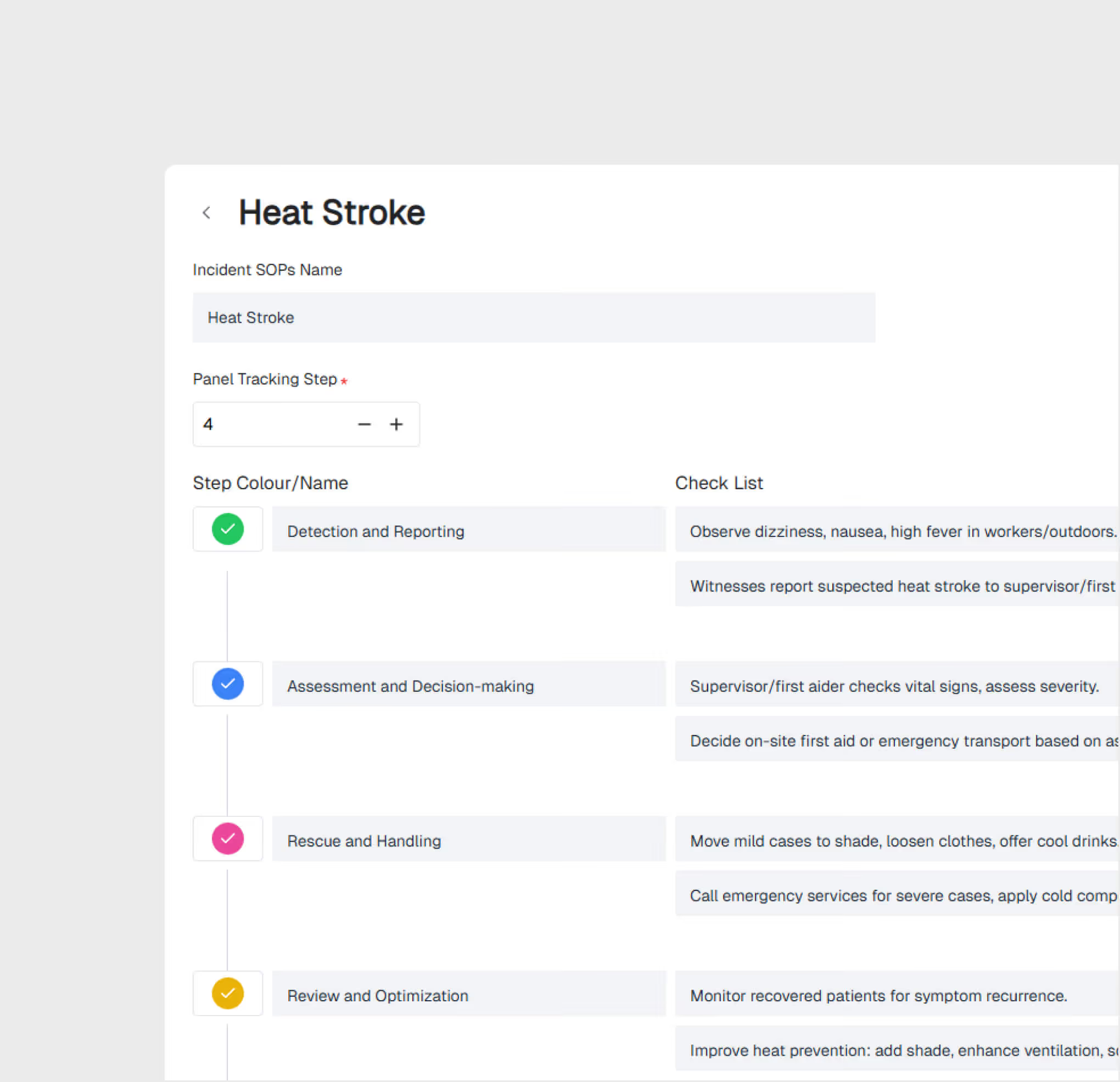
SOP-Driven Investigation Workflows
Geo-Tagged Incident Mapping
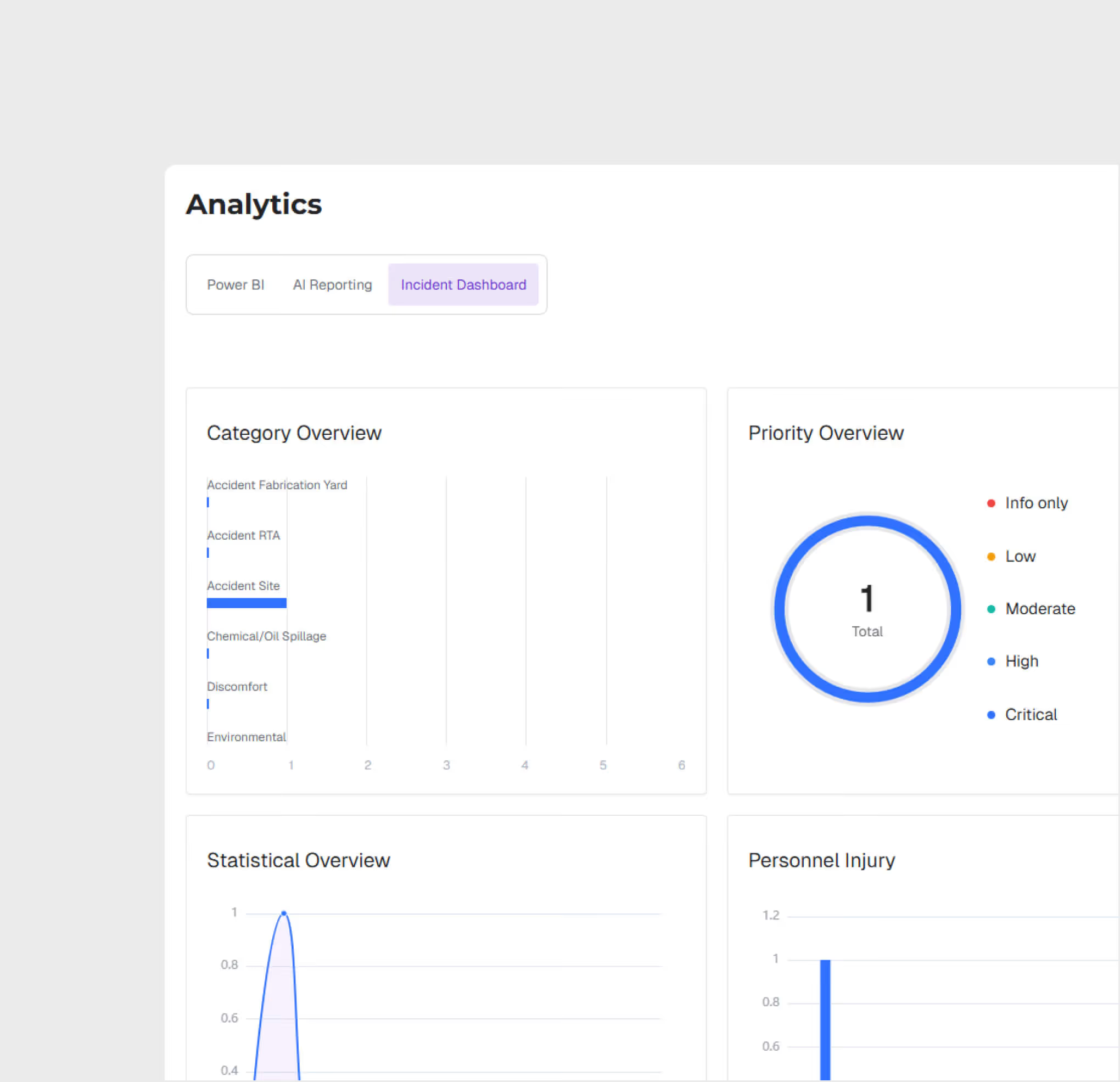
Incident Analytics Dashboard
.avif)
Digital Incident Reporting
Log incidents from the field with structured forms, photo/video evidence, and automatic geo-tagging. Pre-configured templates ensure all required data is captured consistently.
SOP-Driven Investigation Workflow
Trigger standardized investigation workflows automatically based on incident severity. SOPs guide investigators through each step — ensuring consistency and completeness.

Geo-Tagged Incident Visualization
View all incidents on the project GIS map. Identify spatial patterns, high-risk zones, and recurring incident locations for targeted prevention strategies.
Incident Dashboard & Analytics
Track incident trends, response times, resolution rates, and severity distributions. Generate regulatory reports and identify patterns for proactive safety management.
Incident Management is most useful for:
HSE Managers
Incident Lifecycle Oversight
Manage the full incident lifecycle from report to closure, ensure SOP compliance for investigations, and track corrective action completion.
Site Supervisors
Rapid Incident Reporting
Report incidents in the field immediately using mobile forms with geo-tagging and photo evidence — eliminating delayed paper-based reporting.
QHSE Directors
Trend Analysis & Prevention
Analyze incident patterns across the project portfolio, identify systemic risks, and implement preventive measures based on data — not intuition.
"Previously all our incidents were called in across site with no visibility in patterns and areas to improve. With WhiteHelmet Incident Management, we quickly identified the largest areas of improvement and were able to attain an accurate report of incidents per month."
.avif)
Frequently asked questions
Yes. Enterprise clients operating in jurisdictions with specific data transfer requirements can request a DPA. Contact info@whitehelmet.com.
No. WhiteHelmet does not use client-uploaded project data to train AI models without explicit written consent.
Your data remains accessible during any post-cancellation grace period defined in your contract. After this period, data is securely deleted unless otherwise agreed. Contact your account manager for specifics.
WhiteHelmet's AI-generated outputs, including compliance analyses, reports, and observations, are intended to support internal decision-making. They do not constitute certified professional or legal advice. Clients are responsible for verifying outputs with qualified professionals before formal submissions.
WhiteHelmet uses end-to-end encryption, role-based access controls, multi-factor authentication, and continuous monitoring. In the event of a confirmed breach, affected clients are notified in accordance with applicable law.
WhiteHelmet follows OWASP methodology for global security standards and adheres to the National Cybersecurity Authority (NCA) requirements in the Kingdom, and is SOC 2 Type II certified, independently audited based on the AICPA's Trust Services Criteria covering Security, Availability, and Confidentiality.
WhiteHelmet products Incident Management works well with

Field Intelligence
